NIST Framework for Improving Critical Infrastructure Cybersecurity

The Framework for Improving Critical Infrastructure Cybersecurity prepared by the National Institute of Standards and Technology (NIST) against the backdrop of the landscape of standards and regulations in the IT and OT sectors is a unique document. Firstly, they do not constitute a standard guide containing a list of actions necessary to undertake a specific level of cybersecurity. Instead, the framework is a tool to help a company understand its cybersecurity needs by providing a common language to describe, manage, and communicate cybersecurity risks internally and externally. They do it by referring in this process to recognizable standards and norms, incl. ISO / IEC 27001, ISA / IEC 62443 or COBIT 5, but not following them. Second, the framework is the fruit of public-private cooperation. Consultations and revision of the assumptions, conducted between public administration, entrepreneurs and the academic community, led to the publication of the second version of the document (2014, 2018). Third, the NIST framework is a document focused on the market needs of enterprises. At the same time, they focus on using business incentives to properly plan cybersecurity activities. Within NIST, it is the business that defines the role of ITsec activities, not the other way around.
What you’ll find in this article:
- What was the framework for? – the objectives of the NIST framework
- Introduction to the NIST framework – the structure of the framework for increasing the safety of industrial control systems
- How to use the framework? – NIST Framework implementation
What was the framework for?
The goal of the NIST framework is to lower the risk level of an industrial company by aligning the cybersecurity risk management process with the company’s business goals. Although the document in the title refers directly to the critical infrastructure, it was designed to support the improvement of processes in the broadly understood industry. It can be both a tool for improving the existing cybersecurity system, including industrial control systems, and a basis for its thorough reconstruction, even from scratch. At the same time, the framework is not intended to eliminate the risks that are a natural part of any business. According to the applied logic, the risk related to cybersecurity is in this respect no different from the financial risk or the risk related to maintaining the good reputation of the company. Defining your risk tolerance is the first step in prioritizing ITsec activities and investments.
The NIST framework, collecting the standards, norms and good practices existing on the market, creates a single conceptual framework (taxonomy) and a group of recognizable mechanisms that are to help the company in:
1. Description of the current state of cybersecurity in the company;
2. Determining the desired target state in the field of cybersecurity;
3. Identifying the possibilities of improving the current state, using the principle of iterative, repeatable process (continuous improvement);
4. Assessing the progress towards the target state;
5. Conducting communication regarding cybersecurity to internal and external stakeholders – clients, employees, shareholders, officials.
Introduction to the NIST Framework
The NIST framework can be viewed as a toolbox to build, review, and repair a cybersecurity risk management system in an industrial company. The most important of the tools is the “Framework Core”, supplemented by Implementation Tiers and Framework Profile.
Core of the methodology
Provides a list of specific cybersecurity activities and their expected results. These are collated with existing industry standards, guidelines and informative references to enable them to relate to documents or procedures already in use. The core contains three levels of tools:
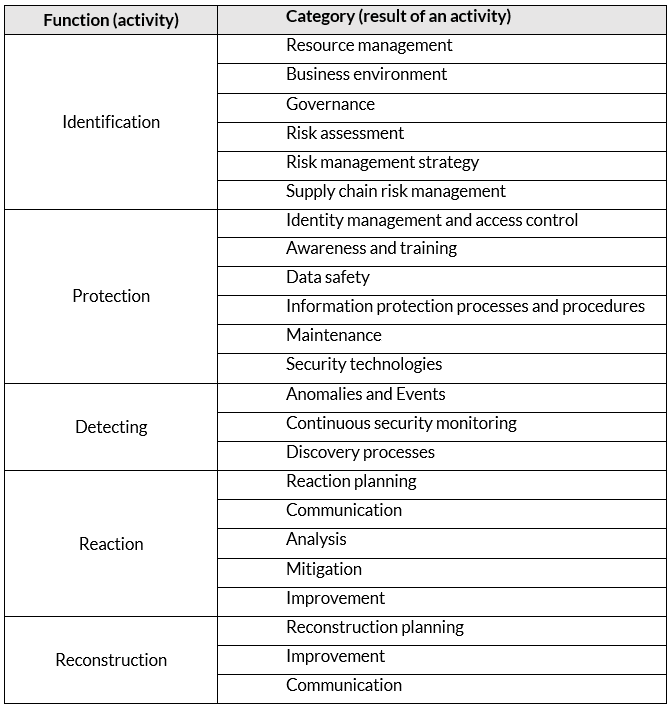
• Features – describe possible cybersecurity activities at the highest level of general. There are five of them: identification, protection, detection, response, and reconstruction.
• Categories – are part of a specific function, grouping the possible results of the actions taken.
• Subcategories – break down categories in more detail into specific results of technical or managerial activities.
Table 1. Core of the NIST Framework for Improving Critical Infrastructure Cybersecurity
Deployment levels
The levels describe the increasing or decreasing degree of stringency and complexity of cybersecurity risk management processes. Not all companies need and should implement the highest levels present in the framework. A move to higher tiers is warranted when a cost-benefit analysis shows a cost-effective reduction of cybersecurity risk. The levels help to determine to what extent risk management is based on the business needs of the enterprise and is integrated with the overall risk management practices of the organization. The framework distinguishes between four possible levels: (1) Partial implementation, (2) risk informed implementation, (3) advanced / repeatable implementation, (4) adaptive implementation.
Profiles
Profiles are conceptual tools that allow the company to translate the “core” (i.e. functions, categories, subcategories) into its specificity and thus to create its unique cybersecurity management profile and adapt cybersecurity activities and goals to business needs, risk tolerance and resources that the organization has. The profile enables organizations to establish a road map to reduce cybersecurity risks. A profile can be used to describe both the current state and the desired target state. Larger enterprises, due to the diverse structure, may decide to select and create many profiles adjusted to, for example, individual departments or branches, taking into account their individual needs.
How to use the framework?
This should be emphasized once again: the NIST framework is not a to-do list. Instead, they are a cybersecurity risk management tool. They are a set of concepts and mechanisms that are to help a company understand and match its level of cybersecurity risk to the place on the market – both in the context of the sector it represents, place in the supply chain, and the specifics of its production process. From this perspective, organizations can use the framework to create a new cybersecurity program or to improve an existing one. There are then seven basic steps:

In line with the graphic emphasizing the cyclical nature of the described process, the NIST framework promotes the logic of iterative, iterative implementation of these activities.
Finally, the framework discussed in this article is just one of many documents created by NIST that entrepreneurs can use to increase their cybersecurity. Another example of a practical and helpful set of knowledge is, for example, the Guide to Industrial Control Systems Security SP 800-82. This document presents specific tools to support cybersecurity, such as intrusion detection system (IDS), inventory tools, the functionalities of which are an integral part of SCADvance XP.
—
If you would like to learn more, please follow our social media accounts for further updates when a new publication is available or sign up to our newsletter.
—
Tags: cybersecurity; cybersecurity for industry, cybersecurity for automation, cyberbezpieczeństwo, cyberbezpieczeństwo dla automatyki, cyberbezpieczeństwo dla przemysłu, SCADA, SCADvance, SCADvance XP, cyberbezpieczeństwo OT, cyberbezpieczeństwo infrastruktury, OT security, critical infrastructure protection, cyberbezpieczeństwo dla infrastruktury krytycznej, nist, nistframework

Request a Demo
Fill in the form. Our experts will contact you to arrange individual tests.
ZAMÓW DEMO